The internet is an incredibly powerful tool. With just a few keystrokes, button presses, or swipes, you can gain access to information on just about any subject. Sometimes, however, you’re researching a sensitive subject that you wish to keep private.
If you’re doing these things on a network owned by someone else, such as a public WiFi network, your data is visible to the owner of the network. Fortunately, there are a number of ways you can hide your browsing activities from a hotspot owner or even your internet service provider (ISP).
Table of Contents

Best Ways of Hiding Your Internet Your Internet History
- Use a Proxy
- Use a VPN Service
- Use the Onion Router (TOR)
- Use your Home Network or Computer as a VPN
- Use Your Mobile Hotspot Instead of Public WiFi
Proxies
Proxies do not hide the IP address that your computer is connected to. Instead, a proxy is a service that essentially browses the web for you. When you use a proxy, you send all of your traffic to the proxy, which then sends it out to the rest of the web. When you use a proxy, your network owner only knows that you’re connected to a proxy. They can’t see what you’re using that proxy to access.
The big downside of using a proxy is that it only protects the traffic that is going through the proxy.
Any other traffic coming from your computer is completely unencrypted, and the hotspot owner can see the traffic in the clear.
We would recommend a proxy if you only want to occasionally hide the activities limited to a single web browser session. Most people would be better off using a VPN rather than a proxy.
VPNs
A VPN is essentially an improved version of the proxy. While a proxy hides your internet traffic through a web browser or a single app, a VPN will encrypt and protect all network activity to and from your computer or smartphone. This means that things like system updates and gaming apps will use the VPN for their traffic, increasing your level of security.
Modern VPN services are designed to minimize the performance impacts of encryption and packet overhead.
Because VPNs encrypt all of your traffic and have many upsides, it’s usually easier to explain a VPN to a network owner than a proxy. If you’re questioned about VPN use, you can simply say that you are using it to connect remotely to your employer or to stream Netflix from a different country.
Remember that your network administrator can still tell how much traffic you’re sending and receiving over the network, even if you are using a VPN. VPNs actually increase your data consumption by about 10% – 15%. This is completely normal but also something to be aware of.
Onion Routing (TOR)
A handful of services and apps offer a solution known as “onion routing”. This offers a few advantages over a simple proxy or VPN.
Onion routing works by sending your internet traffic through a series of hops. Onion routing is very similar to using multiple proxies or VPNs in sequence. This can help add additional security to your traffic.
At each hop, your data only knows that it’s being sent between two proxy servers. The final destination and the place of origin are both encrypted. This makes it very difficult to trace who sent it, what it’s about, or where it’s going.
Onion routing has several downsides. The additional routing hops involved with onion routing make it run much slower than a proxy or VPN. Most websites will load noticeably slower when using TOR. Other things like gaming or watching high-definition videos are next to impossible via TOR.
Some onion routing solutions are complicated or prohibitively expensive. For most people, onion routing doesn’t offer that many advantages of using a regular VPN. A VPN provides a good level of security while not as significantly impacting performance.
Using Your Home Network As A VPN
If you’ve got the technical know-how, it’s not too difficult to use your home network or home computer as a way to get some anonymity on networks you don’t own. Leaving a device such as a PC running in your home can enable you to route internet traffic through it, allowing you to use your own network as a VPN.
There are several ways of doing this. The simplest is to use remote desktop access software to browse the web through your computer at home.
Another option is to purchase a router with built-in VPN server functionality. The Ubiquiti band of routers is an excellent option if you want to get an inexpensive router with VPN server functionality. This is what I personally do. Whenever I travel, I route all of my internet traffic through my home network.
If you do not want to route traffic through your home network or have an IP address that keeps changing, you can set up your own VPN in the cloud. Installing a program like Streisand or Algo VPN to the cloud platform of your choice will enable you to act as your own VPN provider.
Use Your Phone’s Hotspot Functionality
Even if you use a VPN or a proxy, the person who owns the wireless network will still be able to see that you’re using the network and sending data traffic. If you want to be totally invisible, the best way to do that is to connect to a different network entirely.
Try using your phone as a source of internet. In addition to browsing directly on your phone, you can also use the mobile hotspot function to enable your phone to broadcast a small WiFi hotspot that you can connect your other devices to. This can allow you to access the internet without the network owner having any access to your traffic since no data is going across their network whatsoever.
In general, using your phone to provide an internet connection is the simplest and easiest way to ensure that the owner of a WiFi hotspot can see what you’re doing. As long as you get a decent cell phone signal, you will get speeds that are equal to or greater than the speeds offered by most public WiFi networks.
You may want to consider renaming your hotspot to something that doesn’t indicate that it belongs to you.
Who Can See Your Internet Traffic
The ability to track internet activity is not limited to wifi hotspot owners. Anyone with full access to a network can set up that network to do basically whatever they want. Your internet service provider, employer, public WiFi owner, or any other entity providing you with internet can monitor and log your browsing activities. Most ISPs are required by law to keep logs of some user activities.
With a bit of technical know-how, it is not terribly difficult to configure a router to record the internet activities of everyone connected to a given network.
Most network owners are not networking experts. Unfortunately for you, they don’t need to be. Many companies offer software that can track network traffic to varying degrees. This software ranges from basic firewalls that block certain categories of websites to products that can track and record the web traffic of each individual user connected to a network. When you see the terms of service page after connecting to a WiFi hotspot, that page is likely telling you that you are being monitored.
In many cases, network owners are mostly monitoring to ensure that one user doesn’t hog all of the bandwidth, but that doesn’t mean that they’ll never take a look at what individual users are doing or how often they come back to visit. This means that the owner of your local coffee shop doesn’t have to be a tech wizard to see your full search history.

Depending on the type of encryption you use and the amount of information you send, it can be virtually impossible to decipher encrypted internet traffic unless the reader has the key. Many sites and apps use encryption by default (when people talk about SSL or TLS, they’re referring to internet encryption technologies), so it’s likely that you’re already taking advantage of encryption for your web activities.
While encryption on its own won’t hide your internet history from the network owner, it’s a core step in any process that successfully masks your browsing activity and keeps your internet traffic secure. A WiFi owner can see what sites you visit but not what is on these sites because of HTTPS (SSL / TLS).
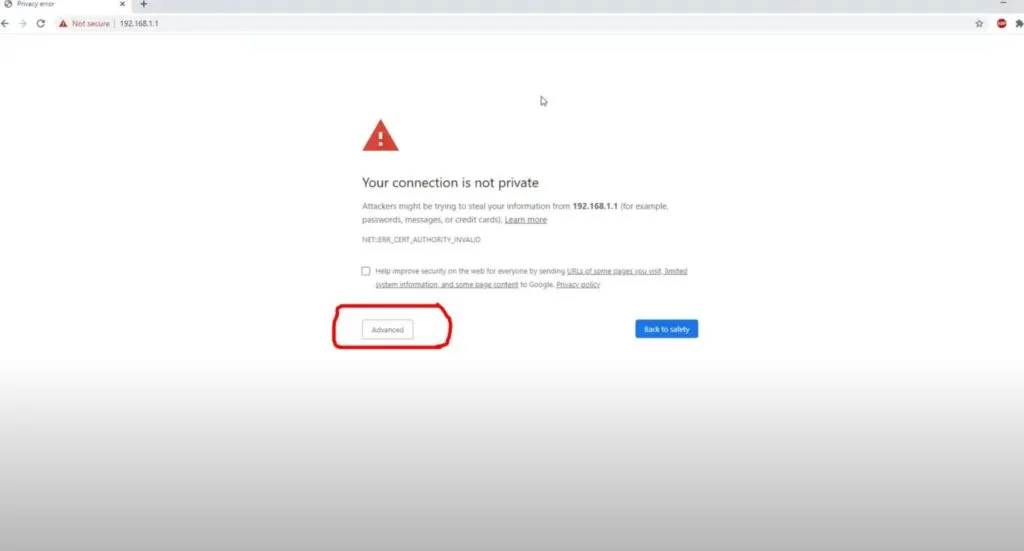
Also, be on the lookout for SSL warnings, as shown in the picture below. These could be a sign of a man-in-the-middle attack. They could also just be signs of an improperly set up captive portal by the public hotspot owner.
Conclusion: How to Hide Browsing History from WiFi Owner
According to the Federal Trade Commission, using public WiFi is probably not the best idea if you care about your privacy. If you really feel the need to use public WiFi, consider not doing anything that you would be concerned about if someone found out about it. A VPN is a great additional layer of security when using public Wi-Fi networks.
If you have a smartphone plan which includes some mobile hotspot data, consider using that in place of public WiFi, as it is a much safer option. It is also likely much faster.
It is also important to note that incognito mode, private browsing, and other browser-based features do not do anything to hide your traffic from a network owner. Changing your DNS settings to use DNS over HTTPS can offer some additional protection but does not fully hide your online activities.
